Today's windows BSOD in the main shopping street of Singapore

Well, this is not technically a BSOD nor even a RSOD, but a Windows startup repair screen on a two-store high screen in the center of Singapore.

Well, this is not technically a BSOD nor even a RSOD, but a Windows startup repair screen on a two-store high screen in the center of Singapore.
Приспичило мне купить пару маек в Сингапуре. А тут лоток с майками по дороге. Беру размер М, иду оплачивать, а тётка на кассе на меня хитро смотрит и заворачивает: иди, мол, разверни и прикинь на тельце. Развернул, прикинул. Потом новую майку развернул и прикинул. В конце концов выбрал XL. Т.е., сингапурский XL.
Two recent news reports cast a shadow on an otherwise shiny picture of Apple. The sudden death of an employee trusted with a prototype of iPhone and the reports of iPods blowing up and causing injuries.
This is the logical outcome of the pressure that is put on Apple employees and subcontractors to deliver top-notch products. This is the price of the Apple lifestyle.
Once in a time, I get to travel to places that make me worry about the data on my laptop. This time, it is not the US, but another openly democratic country where they kill you for a joint, let alone nude pictures. Enough politics, though.
I have a laptop with the /boot in a separate partition, followed by a /root partition and a /swap. Having a separate /boot is mandatory, as the BIOS has to load an unencrypted kernel and its initrd before being able to access the encrypted partition. Another option is to keep /boot on a USB stick, but its setup can take a whole other post.
First things first, let us install software for managing encrypted disks and updating the initrd image:
aptitude install cryptsetup initramfs-tools
We have to make sure that the encryption modules are present on the initrd, so I add the following three modules to the initrd config:
echo aes-i586 >>/etc/initramfs-tools/modules echo dm-crypt >>/etc/initramfs-tools/modules echo dm-mod >>/etc/initramfs-tools/modules
Next step is to inform cryptsetup and inittab of the partition mapping between /dev/hda2 (the physical device) and /dev/mapper/root (its encryption interface).
echo "root /dev/hda2 none luks" >>/etc/crypttab sed -i 's#/dev/hda2#/dev/mapper/root#' /etc/fstab
We also have to change the root device for grub the same way we did it for inittab:
sed -i 's#/dev/hda2#/dev/mapper/root#' /boot/grub/menu.lst
Now, recreate the initrd image by issuing
Отсталая всё-таки страна Россия. Там всё ещё озабочены проблемами коррупции и взяточничества в то время, как весь цивилизованный мир уже *дцать лет использует создание бизнес-ниш из воздуха как основной приём для повышения благосостояния власть придержащих.
Давайте я расскажу про бельгийский опыт на примере titres-services. Очень простая модель. Кое-какие силы в бельгийских органах власти протолкнули проект по прикрытию чёрного рынка работ по уборке дома, глажке, покупке продуктов и создали вид лицензированной деятельности под названием titres-services, что можно перевести на русский скажем как "талоны на уборку".
Самый простой способ задавить конкурента -- бешено демпинговать, что государство и сделало, выделив полмиллиарда евро в 1-й год на финансирование отрасли. Была выбрана компания дле печати талонов (первый откат), которые продавались населению по 6,70 €. Население могло продолжать оплачивать домработниц по-чёрному, тратя в среднем 8 евро в час, либо по талонам, тратя 4,69 € (2,01 € возвращалось путём уменьшения налогов). Конторам, получившим лицензию на работу по талонам, за каждый талон государство выплачивало 21 € через компанию, занимающуюся приёмом талонов (второй откат). На следующий год сумма эта уменьшилась до 20 €, ещё через пару лет составила 18 €.
Наихудший менеджер — это тот, кто считает себя технарём, но уже им не является.
© я
Nowadays, conferences are being run using a century-old approach that puts a lot of trust into the reviewers and the program committee.
However, examples of successful social networks like Slashdot, Digg and Reddit show that it is possible to implement an system that trusts none but works well enough to push up the most insightful texts.
The modification of the evaluation processes shall evolve over at least three stages.
First, an existing system shall introduce the ability to review the reviewers, that is, vote for the quality of reviews and thus -- for the quality of the work done by a particular reviewer. This will allow to rebuild trust in the reviewers in a transparent way.
Once the reviewers are less of a problem, the major attack should be done on the selection itself. The only reason that only a handful of submissions are published among the others is the limited amount of space in the printed journal. It is time to allow everyone to publish their papers on the conference website, ranked by the reviews, so that the selection is gradual, instead of binary. Until paper publications naturally die out, a cutoff ratio or number can be kept.
The last and the most difficult stage is to abandon the reviews by dedicated reviewers all together and move onto the review by peers where everyone who publishes can review peers in the same conferences openly. A fair share of meta-reviewing is expected for this system to keep up against abuse.
Here is a fictitious story of a business client that orders software for a mobile phone to an embedded developer.
Take such a trivial feature of a mobile phone as a the possibility to store last calls. What do you know about it besides that it allows to view last incoming and outgoing calls? This is the level of knowledge that a typical client has and he will express it as a requirement the same way:
— I want that my mobile phone software to store last incoming and outgoing calls.
The developer has two choices: either assault the client with question based on unconfirmed assumptions or tacitly do exactly what was asked. He writes code that keeps two lists ordered by the call time, one list for incoming calls, another one — for outgoing calls.
Soon after, the client finds out that a competing company uses a different design and demands the software to display:
Unfortunately, the previous code has already been written and is linked tightly to the UI code and to the rest of the mobile phone's OS.
So, instead of scapping the previous design and starting from scratch, the developer is now bound to implement new data structures that consists of one new list that combines incoming and outgoing calls in the right order to satisfy the first additional requirement, and three more lists for each of the 2nd, 3rd and 5th additional requirements.
This seems like nothing, but coupled to the synchronization code and error handling code, the result is likely to look cryptic for everyone, including its own developer.
Я — авторитарный демократ. Верю в здоровую конкуренцию автократий за человеческий капитал.
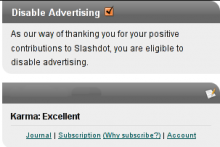
А вот так слэшдот решил поощрять пользователей с высокой кармой. Приятно, что во времена повальной монетизации не все контент-провайдеры видят в пользователе одну лишь дойную корову.